...unless you really like writing engines, which I do.
I never got around to posting about this project since I was kind of waiting for it to be something cooler, but a couple of years in of working on it once in a while the amount of work left kind of hit me. In the depths of my broken animation blending code I was like "wait, what am I even doing here? this is not even close to being a dungeon crawler" So behold: "Frosting", another one thrown on the pile of unfinished engines!
The genesis of this project started back before I had spent time with Unreal and had only really worked on the NV-in-house engine and Cryptic's engine. The NV engine or "NVDemo" as we called it had pretty advanced rendering features since our projects were maybe 85% rendering/shader code, 10% menus, 10% demo/attract mode logic, but it didn't have much in the way of anything else and it was geared towards small scenes, so no real streaming, networking, game logic, etc.
I happened to come across an article about the high-level design of the Unreal 1 networking architecture (since eaten by the internet) and thought "wow this is a whole other can of worms than what I've worked on so far!" also I found this article on draw call management Order your graphics draw calls around! Doing it exactly like this doesn't make much sense in the era of Vulkan and friends, but at the time it seemed fancy. Plus, I didn't like this thing, or that thing with our system at work and wanted to try my crack at a clean slate.
My goal was to build a realtime hack-and-slash rougelike, but mostly I just got a bunch of test levels and crates you can knock over 🙂 Since I knew the least about the non-graphics stuff I started with that which is why the rendering is so basic, no shadows, directional light etc. Otherwise I might accidentally make a rendering engine again and end up with no gameplay. I didn't really get that far but it had some neat features:
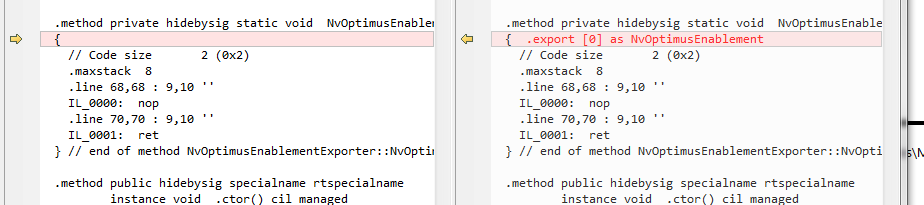
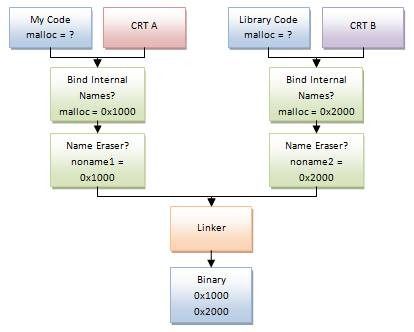
- Serialization and replication/diffing of C++ objects without running a custom preprocessor, mostly as a challenge after using NVDemo and UE
- Command buffer-ish rendering architecture
- Fancy GUI editor "Cobbler" (everything is dessert themed for some reason I can't remember) with full undo/redo using said serialization system
- Reliable unicast/multicast RPC method calls, and reliable/unreliable property replication
- Network games that work both with a headless dedicated server, and player server
- Bullet for physics, which also replicate (mostly because it's not NVIDIA PhysX...learning stuff!)
- Play-in-editor mode. the editor is a server you can connect to. When not PIE you're a spectator, watch designers place things! (ok this feature basically came for free)
- Streaming and hot reloading everything textures, models, animations, prefab definitions, fonts, shaders
- Generic sockets, skeletons. Parent components to sockets on skeletal meshes, physics bodies. Attach random stuff together!
But who knows? Maybe one day it might get a real lighting system and a D3D11 -> Vulkan port.